As organizations grow and expand, they generate large amounts of data and logs from various sources such as applications, systems, and networks. Managing these massive volumes of data and logs can be a daunting task, especially when trying to extract valuable insights to make informed decisions and mitigate potential threats. This is where Next-Gen SIEM comes into play.
The Challenge of Managing Data and Logs in Modern Organizations
Managing data and logs can be a daunting task for organizations, particularly those dealing with large volumes of data from disparate sources. However, the data and logs provide valuable insights into performance, risks, and growth. They help organizations make informed decisions, identify potential threats, and optimize their operations.
For example, data and logs can help identify network anomalies, user behavior, and suspicious activity. Without effective data and log management, organizations may miss critical insights and expose themselves to cybersecurity risks. However, managing this data and logs can be a significant challenge for businesses. Below, we will explore the key challenges organizations face when it comes to managing data and logs.
- Volume and Velocity: The sheer volume and velocity of data and logs generated by modern organizations can be overwhelming. With the increasing adoption of cloud computing, IoT devices, and other technologies, the amount of data generated can be massive. Managing and analyzing all of this data in real-time can be a significant challenge.
- Security and Compliance: The security and compliance challenges associated with managing data and logs are becoming more complex. Organizations need to ensure that their data and logs are secure from unauthorized access and comply with various regulatory requirements, such as GDPR, HIPAA, and PCI-DSS.
- Access and Collaboration: In many organizations, data and logs are siloed in different departments, making it difficult for employees to access and collaborate on this information. This can lead to inefficiencies and missed opportunities for insights.
- Cost: The cost of managing data and logs can be a significant challenge for many organizations. This includes the cost of storing and processing data, as well as the cost of hiring skilled professionals to manage this information.
The Role of Next-Gen SIEM in Data and Log Management
Next-Gen SIEM (Security Information and Event Management) is a modern solution for collecting, storing, and analyzing data and logs. It differs from traditional SIEM solutions in its ability to handle large volumes of data, real-time threat detection and response, automated incident response, and advanced analytics.
Next-Gen SIEM solutions provide a more holistic approach to security by integrating threat intelligence, vulnerability assessment, and risk management. With Next-Gen SIEM, organizations can detect and respond to threats faster, and gain valuable insights into their security posture. The following are some of the most important roles of Next-Gen SIEM in Data and Log Management.
- Streamlining Data Collection and Analysis: Next-Gen SIEM can collect and analyze data from a wide range of sources, including cloud-based applications, mobile devices, and IoT devices. This helps organizations gain comprehensive visibility into their security posture and identify threats more quickly.
- Automating Threat Detection and Response: Next-Gen SIEM uses machine learning and automation to detect threats in real-time, reducing the need for manual intervention. This helps organizations identify and respond to threats more quickly, reducing the time it takes to mitigate potential damages.
- Improving Compliance and Auditing: Next-Gen SIEM can help organizations meet regulatory compliance requirements by collecting, analyzing, and reporting on security-related events. This includes monitoring user activity, access logs, and other security-related data.
- Enhancing Incident Response Capabilities: Next-Gen SIEM provides advanced analytics and automation capabilities that can help organizations respond to security incidents more quickly and effectively. This includes identifying the root cause of an incident, prioritizing response efforts, and facilitating the incident response process.
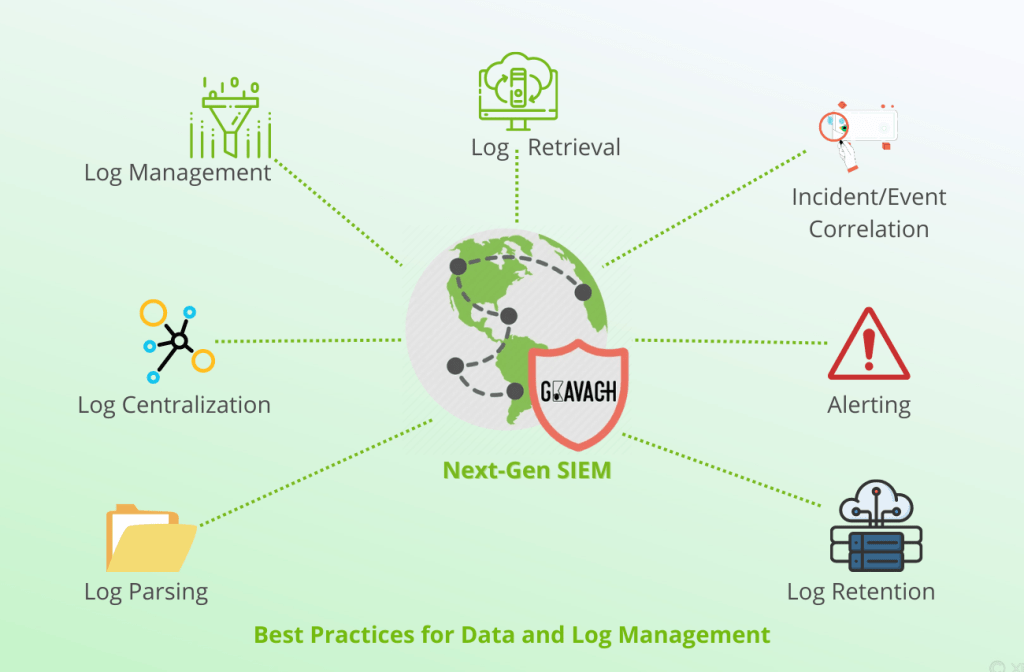
Best Practices for Data and Log Management
To get the most out of data and log management, organizations should follow some best practices, such as:
- Collecting and Storing Data and Logs: Data categorization, storage architecture, and data retention policies are crucial for effective data and log management. Organizations should ensure that they have a consistent approach to collecting and storing data and logs. They should also categorize data and logs based on their sensitivity and relevance.
- Analyzing Data and Logs: To gain insights from data and logs, organizations need to use advanced analytics techniques such as machine learning algorithms, correlation rules, and behavioral analysis. These techniques can help organizations identify anomalies and patterns that may indicate potential threats.
- Monitoring and Reporting: Organizations should monitor and report on security events, data access, and compliance. This can help organizations detect and respond to threats faster and meet regulatory compliance requirements.
- Perform Regular Audits and Assessments: Regular audits and assessments of data and log management processes can help organizations to identify potential vulnerabilities and areas for improvement. These audits can be used to assess data protection, data access controls, data retention policies, and compliance with regulations and industry standards.
- Ensure Data Security and Encryption: Data security and encryption are critical to effective data and log management. Organizations should implement a strong data security strategy that includes data encryption, user access controls, and secure data transfer protocols. This can help to reduce the risk of data loss and security breaches, and improve compliance with regulations and industry standards.
Addressing Concerns about Data Security and Privacy
Data security and privacy are critical concerns for organizations of all sizes. They need to ensure that their data and logs are secure and comply with regulatory requirements. The rise in cyberattacks and data breaches has made it increasingly challenging for companies to protect sensitive data and comply with data privacy regulations. Next-Gen SIEM solutions can help organizations address these concerns by providing advanced security features such as access control, encryption, and monitoring. Next-Gen SIEM solutions also facilitate organizations in meeting regulatory compliance requirements by monitoring and reporting on security events and data access.
Conclusion
In conclusion, effective data and log management is critical for organizations to identify potential threats, optimize their operations, and meet regulatory compliance requirements. Next-Gen SIEM solutions provide a modern approach to data and log management, enabling organizations to collect, store, and analyze data and logs more efficiently. By adopting best practices for collecting, storing, analyzing, monitoring, and reporting on data and logs, organizations can leverage Next-Gen SIEM solutions to maximize the value of their data and logs.
Therefore, we encourage organizations to take action and implement best practices to manage their data and logs effectively. Additionally, we urge them to consider Next-Gen SIEM solutions to help them collect, store, and analyze data and logs more efficiently. By doing so, organizations can gain valuable insights and respond to potential threats in real-time, improving their overall security posture.