GKavach is simply a combination of two different words G and Kavach, “G” comes from it’s creator company’s name Green Tick Nepal Pvt. Ltd. where as “Kavach” meaning “Armor” a “shield” in Sanskrit.
Why GKavach, Not Others?
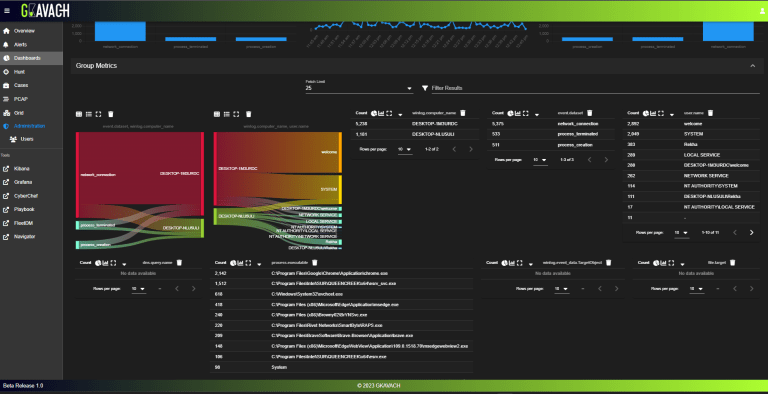
Smart Log Management
Offers controlled log analysis, custom field enrichment, fast parsing, and flexible retention policies.

Powerful Threat Detection
Utilizes behavioral analytics and integrated threat intelligence to detect unusual activities and stay ahead of new attacks.
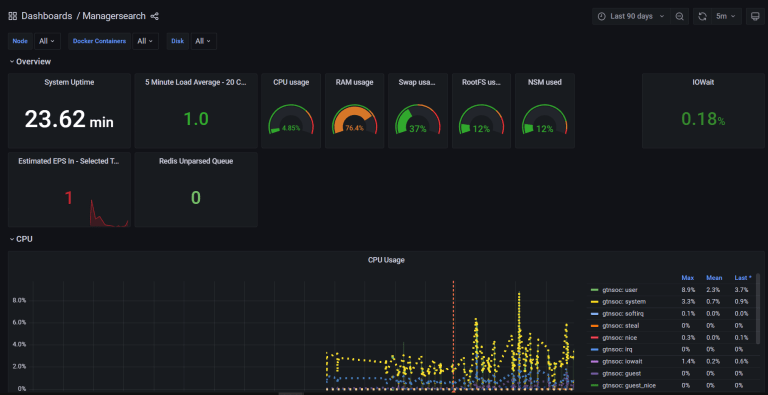
Clear, Actionable Insights
Provides comprehensive security dashboards with attack visualizations, custom rules, and pre-built threat detection sets.
Streamlined Incident Response
Features seamless ticketing integration, automated workflows, and detailed analysis tools for faster incident resolution.
Local Expertise, Global Standards
Developed in Nepal with an understanding of local needs, while meeting international security benchmarks and providing dedicated local support.